The Veil of Tor: Navigating the Labyrinth of Anonymity in the Digital Age
In the shadowed corridors of the digital realm, a browser named Tor stands as a sentinel of privacy, weaving a complex tapestry of encryption and obfuscation. Yet, as of 2026, this guardian, while formidable, does not operate in absolute secrecy. Your Internet Service Provider (ISP) perceives the act of your connection to its network—a beacon of encrypted traffic pointed toward a known gateway—though the intimate details of your digital pilgrimage remain shrouded in layers of cryptographic mist. This duality forms the core of Tor's enigmatic existence: a powerful tool for anonymity that simultaneously casts a recognizable silhouette against the backdrop of the monitored internet.

The Onion's Architecture: A Triad of Concealment 🧅
At its heart, the Tor network functions as a digital labyrinth, routing user traffic through a meticulously orchestrated sequence of servers before it reaches its ultimate destination. This process, poetically termed "onion routing," encapsulates data within three distinct layers of encryption. Your journey begins not with a single step, but with a triple-wrapped parcel, each layer destined for a specific guardian in the chain.
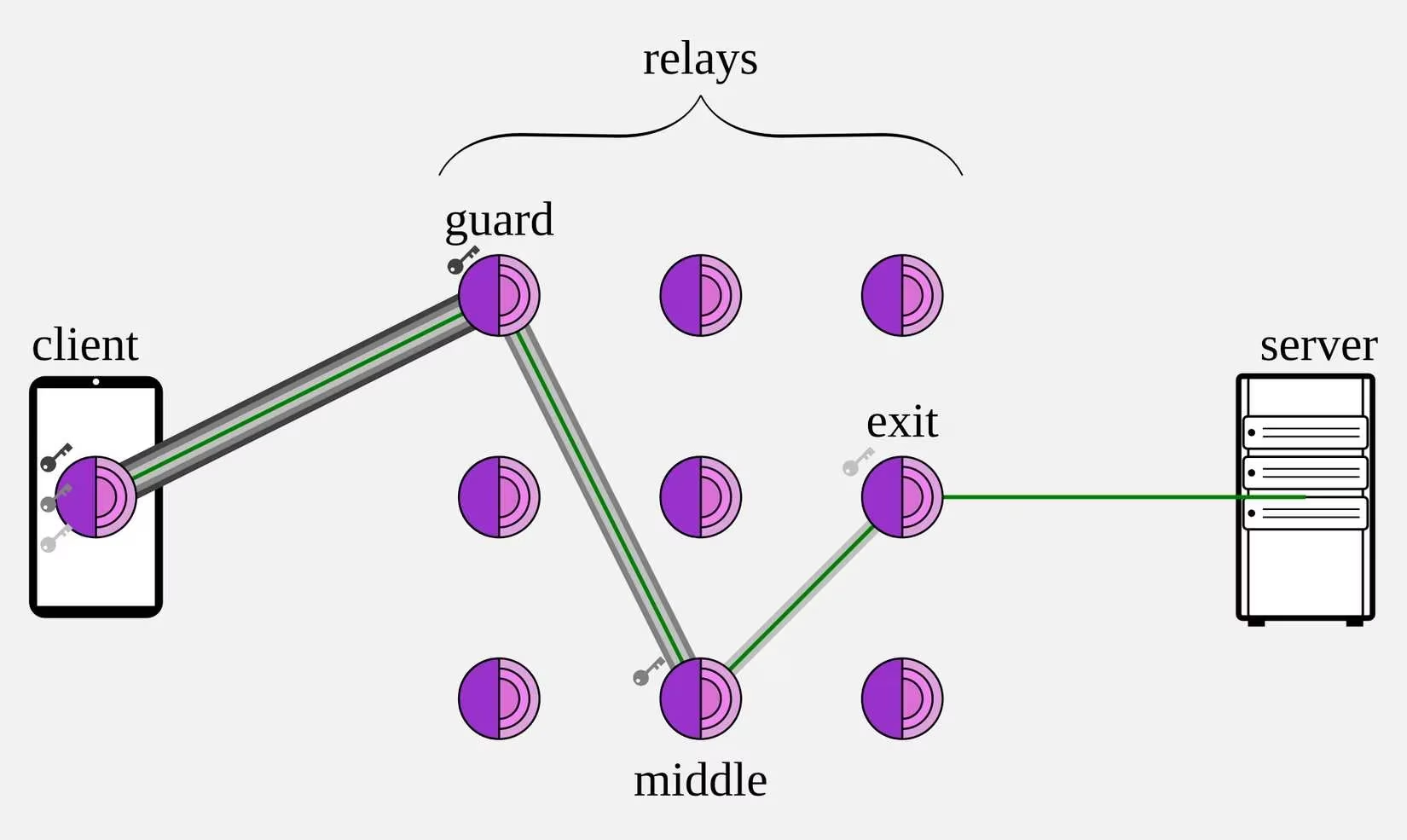
The path is navigated by three distinct types of nodes, each playing a crucial, yet isolated, role:
| Node Type | Role & Knowledge | Analogy |
|---|---|---|
| Entry/Guard Node | Receives the initial, triple-encrypted data. Knows your IP but not the final destination. Removes the outer layer. | The gatekeeper who sees who arrives but not where they go inside. |
| Middle/Relay Node | Receives partially decrypted data. Knows only the previous and next hop. Removes the second layer. | The courier in a sealed tunnel, aware only of the immediate stations. |
| Exit Node | Receives the final, single-encrypted layer. Decrypts it and forwards the request to the public web. Its IP is what the target website sees. | The final messenger who delivers the letter, wearing the network's mask. |
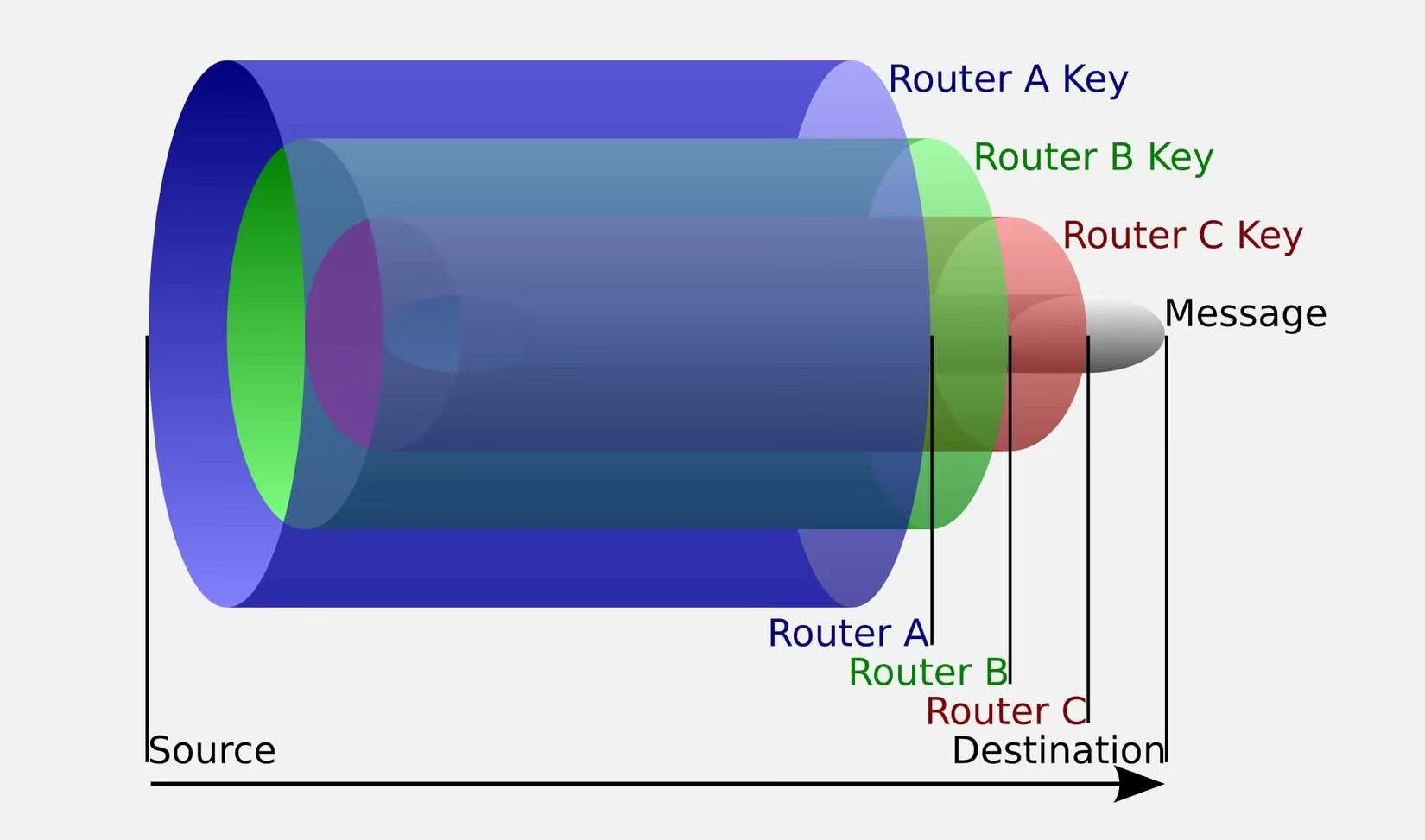
This elegant choreography ensures that no single entity comprehends the entire voyage. Your ISP witnesses only the initial encrypted connection to a publicly listed Tor entry node. The destination website, in turn, perceives only the IP address of the exit node, a digital mask that obscures your true origin. The encryption employed is so robust that even if intercepted, the data appears as an indecipherable symphony of noise, revealing nothing of the content within—be it a search query, a message, or a login credential.
The ISP's Gaze: Perceiving the Shadow, Not the Form 👁️
While the sanctum of your activity is protected, the aura of your connection is not entirely invisible. Your ISP possesses a form of digital perception that discerns certain meta-patterns:
-
Connection Signature: It can definitively identify that you are utilizing Tor by recognizing connections to the network's publicly cataloged entry nodes.
-
Traffic Volume & Timing: It observes the quantity of data transmitted and received, alongside the chronology of your sessions—when you connect, for how long, and the approximate data flow.
This constellation of metadata sketches a silhouette of your usage but fails to illuminate the specific contours of your actions. It knows the when and the how much, but crucially, not the what or the where. The ISP remains blind to:
❌ The specific URLs you visit.
❌ The content you view or download.
❌ Your communications, searches, or any sensitive information transmitted.
Weaving a Deeper Veil: The Synergy of Tor and VPN 🔒
For those seeking to obscure even the silhouette of their Tor usage, a common strategy involves layering technologies. Employing a reputable Virtual Private Network (VPN) prior to connecting to Tor creates an additional cloak. In this configuration:
-
Your device first establishes a secure, encrypted tunnel to the VPN server.
-
All subsequent traffic, including the connection to the Tor network, flows through this tunnel.
-
Your ISP now only perceives a connection to a VPN server—a common and less conspicuous type of traffic—effectively masking your affiliation with the Tor network entirely. This amalgamation transforms your digital footprint into what appears to be ordinary, privacy-focused browsing.
Navigating the Realms: Legality, Community, and Practicality ⚖️
As of 2026, Tor remains a lawful instrument in numerous nations, including the United States, cherished by a diverse congregation of legitimate users:
-
Journalists & Activists: Protecting sources and communications in hostile environments.
-
Privacy Advocates: Resisting pervasive surveillance and data harvesting.
-
Everyday Citizens: Seeking refuge from intrusive tracking and profiling.
However, the journey through Tor's labyrinth is not without its tolls and potential perils:
-
Performance Toll: The circuitous path through multiple nodes imposes a significant cost in speed, making browsing noticeably slower than conventional internet access.
-
Access Barriers: Some websites and services actively block traffic originating from known Tor exit nodes, creating digital dead-ends for users.
-
Jurisdictional Shadows: A handful of nations with stringent encryption laws—such as China, Russia, and Iran—may prohibit or heavily monitor its use. The onus is always on the traveler to understand the local digital landscape.
-
Operational Vigilance: The strongest privacy guarantees come from using the official Tor Browser, designed to prevent configuration errors. Alternative methods demand rigorous technical hygiene to avoid accidental exposure.
The Poetic Conclusion: An Imperfect Sanctuary
Tor stands not as an impenetrable fortress, but as a sophisticated sanctuary within the networked world. It is a testament to the human desire for agency and confidentiality in the digital age. It excels at severing the direct link between identity and action, hiding the content and destination of one's voyage. Yet, it cannot render the voyager completely invisible; the act of embarking on the journey itself leaves a ripple.
Therefore, the wise navigator understands Tor not as a solitary shield, but as a potent component within a broader tapestry of privacy. It is a tool for specific passages—a way to whisper in a crowd, to observe without being cataloged, to move with purpose while leaving a blurred trail. In the endless dance between surveillance and secrecy, Tor provides crucial steps, but the entire choreography of digital safety requires continuous awareness, layered strategies, and an acceptance of the nuanced, rather than absolute, nature of online anonymity.
