The New Digital Wild West: How Scammers Are Using AI and Psychology to Steal Billions
In 2024, scammers pulled off a staggering heist, walking away with a cool $16.6 billion. Fast forward to 2025, and the landscape is even more treacherous, a veritable digital minefield where old cons have gotten a high-tech makeover. It's not just about dodgy emails anymore; it's a full-blown psychological war where criminals leverage artificial intelligence, social engineering, and deep emotional manipulation to separate you from your money. From AI-powered voice clones that sound exactly like your boss to fake romances that tug at your heartstrings, the game has changed, and knowing the rules is no longer optional—it's essential for survival.
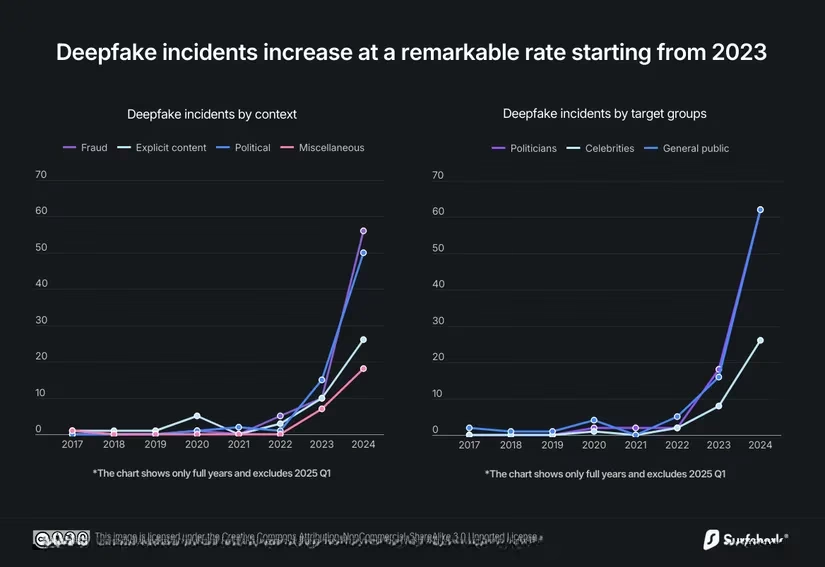
Remember those hilarious Instagram reels of babies having full-on conversations? That's deepfake tech, and it's not just for laughs. According to the FBI, threat actors are now using AI to generate fake audio and video that's nearly indistinguishable from the real thing. A Surfshark report shows these deepfake scams, targeting both celebrities and everyday folks, have been increasing at an alarming rate since 2023. It's a whole new ball game where seeing and hearing is no longer believing.
The modus operandi is impersonation at scale. Imagine getting a call from your CEO's voice, sounding stressed, demanding an urgent wire transfer to close a critical deal. That's the reality. The tech has become so accessible that creating a convincing voice clone requires just a few seconds of audio. Financial losses from these AI-driven scams skyrocketed by 33% from 2023 to 2024, hitting that $16.6 billion mark. Scammers create a sense of urgency through every channel—calls, emails, video messages—pushing victims to make snap decisions without a second thought. It's a high-pressure sales tactic from hell.
The Emotional Predators: Romance Scams 2.0
If deepfake scams are about impersonation, romance scams are about infiltration—of your heart and wallet. These emotional predators have earned their reputation by targeting people at their most vulnerable. A Barclays report noted a 20% rise in romance scam reports in early 2025, with scammers specifically hunting for those who've recently experienced personal loss. It's a lowdown, dirty trick.
Their playbook is chillingly consistent:
-
The Meet-Cute: They find you on Tinder, Facebook, or slide into your DMs on Instagram.
-
The Shift: After a few days, they'll ask to move to WhatsApp. 🚩 Major red flag!
-
The Long Con: This is where they put in the work. Daily "good morning" texts, stolen profile photos, remembering your birthday—they're building the illusion of a real connection.
-
The Excuse: They always have a reason they can't meet. Oil rig worker, deployed military, international businessman—always far away with a plausible story.
-
The Ask: Once trust is built, the financial requests start. It begins small ("help with my phone bill so we can keep talking") and escalates to "emergencies"—medical bills, travel money to meet, or "can't-miss" investment opportunities for your future together. Victims often rationalize the red flags because of their emotional attachment. It's a classic case of the heart ruling the head.
Spotting these scams is straightforward if you keep your wits about you:
-
Never move conversations off a dating platform early on.
-
Anyone who can't video chat or meet in person after a reasonable time is suspect.
-
Anyone asking for money, regardless of the story or your feelings, is 99.9% likely running a scam. Period.
Crypto Chaos: The Riskiest Game in Town
Move over, old-school fraud; crypto scams are now the worst of the bunch. The Better Business Bureau crowned them the riskiest fraud type in 2024, and they're still going strong. According to Chainalysis, these scams are brutally effective because they attack from two angles: the promise of easy money (FOMO - Fear Of Missing Out) and the panic that you'll miss "the next Bitcoin" if you don't act fast.
How do they hook you? 🤔
| Entry Point | Method | The Hook |
|---|---|---|
| Social Media Ads | Fake investment ads on Facebook/Instagram. | Promises of tripling your money in weeks after you share contact info. |
| Dating App Pipeline | A romantic connection slowly pivots to crypto advice. | "Hey, I've been killing it with crypto, you should try this platform." |
| Account Takeover | A hacked friend's account messages you. | "Check out this amazing investment opportunity!" Looks legit because it's from a friend. |
The scam involves directing you to incredibly sophisticated fake trading platforms. These sites look professional, show fake but convincing portfolio growth, and even allow small withdrawals to build trust—a tactic known as "the taste." The house of cards only collapses when you try to withdraw a larger sum and find the money, and the "advisor," have vanished into thin air.
Golden Rule: Always verify any investment platform through multiple independent sources. Never invest based solely on a social media ad or a message, even from a known contact.
The Evergreen Threat: Phishing Gets an AI Upgrade
Phishing is the old dog that learned terrifying new tricks. It remains highly effective because it exploits human psychology, not software flaws. The 2025 Data Breach Investigations Report still flags it as a top threat, with attackers now using AI to craft perfectly grammatical, highly deceptive messages.
Phishing isn't just email anymore; it's a multi-channel assault:
-
Smishing: Phishing via SMS.
-
Vishing: Phishing via voice call.
-
Angler Phishing: Targeting users on social media.
-
Spear Phishing: Highly personalized attacks using info from data breaches.
The success formula is manufactured urgency: "Your account will be closed in 24 hours!" "Confirm your package delivery now!" "Suspicious activity detected!" The messages look legit, often using real logos and formatting.
Your Defense Kit:
-
Enable Multi-Factor Authentication (MFA) everywhere. This is your single best defense. If they get your password, they still can't get in.
-
Scrutinize sender addresses. A message from "Amazon Support" via a Gmail account is a dead giveaway.
-
Never click links in unsolicited messages. Go directly to the company's official website by typing the URL yourself.
Too Good to Be True: The Online Shopping Trap
Just the other day, my dad was about to fall for a classic one: a luxurious wooden relaxation chair advertised online for an unbelievable $49! The site looked pro, the reviews seemed real, and a countdown timer ticked away, creating that urgent, "buy now or miss out" feeling. To me, it screamed scam, but to many, it's a tempting deal.
These fake furniture sites are part of massive purchasing scams. Scammers use targeted social media ads for luxury goods, electronics, or hard-to-find items to lure in specific demographics. The site takes your money and either sends a counterfeit product or, more often, nothing at all.
Before you click "Buy Now":
-
Research the seller. Google the company name + "scam" or "reviews."
-
Look for clear return policies and legitimate contact information (a physical address, not just a contact form).
-
For big purchases like buying a car online, extreme caution is needed. Scammers create elaborate fake listings for vehicles that don't exist.
Authority & Fear: The Impersonation Scam
These scams work by exploiting two powerful levers: trust in authority and fear of consequences. Scammers pose as IRS agents, police, your utility company, or Microsoft tech support.
-
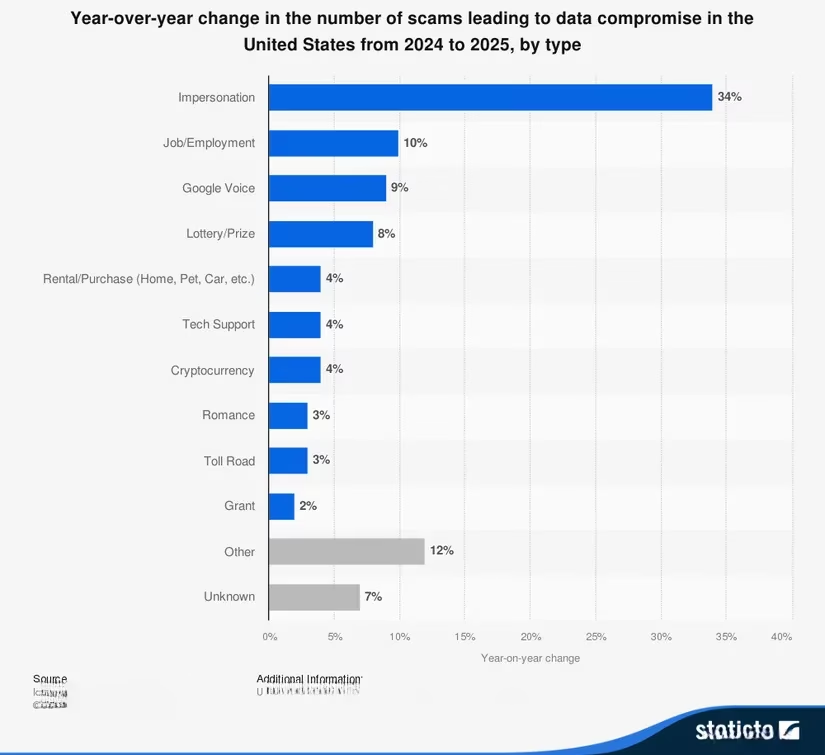
Government Impersonation: "You owe back taxes and will be arrested if you don't pay immediately via gift cards!" They use caller ID spoofing to make the real IRS number appear on your phone. Statista reports a over 30% rise in these scams from 2024 to 2025.
-
Tech Support Scams: A scary pop-up claims your computer is infected. You call the "support" number, and they trick you into giving remote access or paying for unnecessary "services."
They often use personal info from data breaches (your address, partial SSN) to sound credible before launching into high-pressure threats.
Remember:
-
Government agencies will NEVER demand immediate payment via gift cards, wire transfers, or cryptocurrency.
-
Legitimate tech companies do not make unsolicited calls about viruses on your computer.
-
If someone calls claiming a family member is in trouble, hang up and call that family member directly on a number you know is theirs.
The Bottom Line in 2025
AI tools are a double-edged sword, and in the hands of scammers, they're blurring the lines between obvious cons and sophisticated attacks. The barrier to entry is gone; anyone can generate professional phishing emails or clone a voice.
The mantra for the modern age is trust, but verify. Always question unsolicited contact. Verify requests through independent channels (call the company back using a number from their official website). Legitimate organizations do not use pressure tactics to force immediate action. Taking those few extra minutes to double-check isn't paranoia—it's the difference between protecting your hard-earned cash and becoming another statistic in the billion-dollar scam economy. Stay sharp, folks. The digital wild west is only getting wilder. 🤠
