The Illusion of Privacy: Reassessing Trust in the Modern VPN Landscape
In the year 2026, the digital realm remains a labyrinth where every click, every search, and every connection leaves a faint, indelible trace. For the conscientious netizen, the promise of a Virtual Private Network (VPN) has long been a beacon of hope—a shimmering veil cast over one's online identity to obscure the prying eyes of trackers, advertisers, and unseen third parties. Yet, beneath the glossy marketing and the reassuring mantra of 'no-logs,' a more complex and sometimes disquieting narrative unfolds. It is a story not of absolute security, but of nuanced trust, corporate consolidation, and the ever-widening gap between user expectation and technical reality.
The Fragile Promise of 'No-Logs'
The cornerstone of VPN trust is, and has always been, the no-logs policy. To the average user, this term conjures an image of digital amnesia—a service that sees your data flow through its servers like water through a sieve, leaving no record, no memory, no evidence of your passage. It is the ultimate privacy guarantee: if there is nothing to hand over, then not even a court order can compromise your anonymity. 🛡️
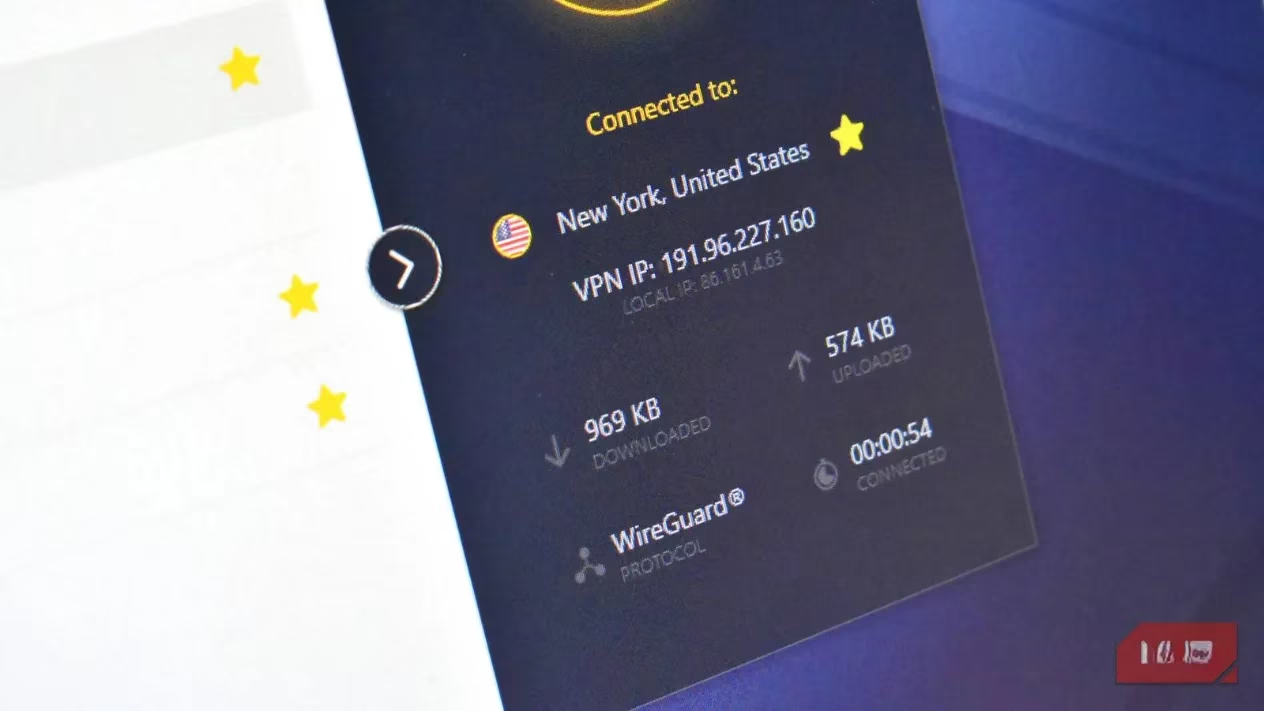
However, the industry's history reveals that this promise can be a spectrum, not a binary truth. The 2017 case involving PureVPN serves as a seminal lesson. The provider, which claimed a no-logs policy, assisted the FBI in a cyberstalking investigation by providing connection logs. These logs, containing user timestamps, became the critical link that, when cross-referenced with data from other companies like Google, identified a suspect.
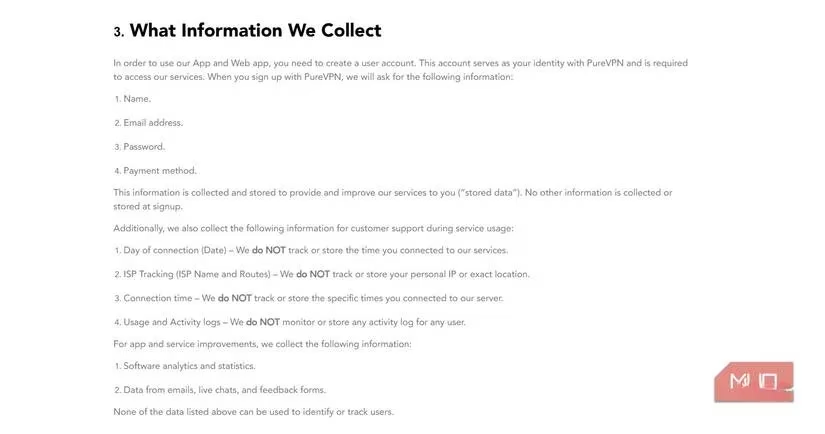
This incident illuminated a crucial distinction often buried in fine print:
-
User Expectation: 'No logs' means no data collection whatsoever—no browsing history, no connection times, no IP addresses.
-
Provider Reality: 'No logs' may mean no browsing logs, but retention of 'network,' 'troubleshooting,' or 'maintenance' logs (timestamps, bandwidth usage, etc.).
While such metadata may seem innocuous to a provider, in the hands of a determined entity with access to other data sets, it can complete a puzzle. PureVPN, to its credit, underwent independent audits post-2017 to rebuild trust and now asserts a verified no-log stance. Yet, the episode exposed a systemic lack of a universal, enforceable standard for what a 'no-logs policy' must entail.
The Veil of Corporate Consolidation
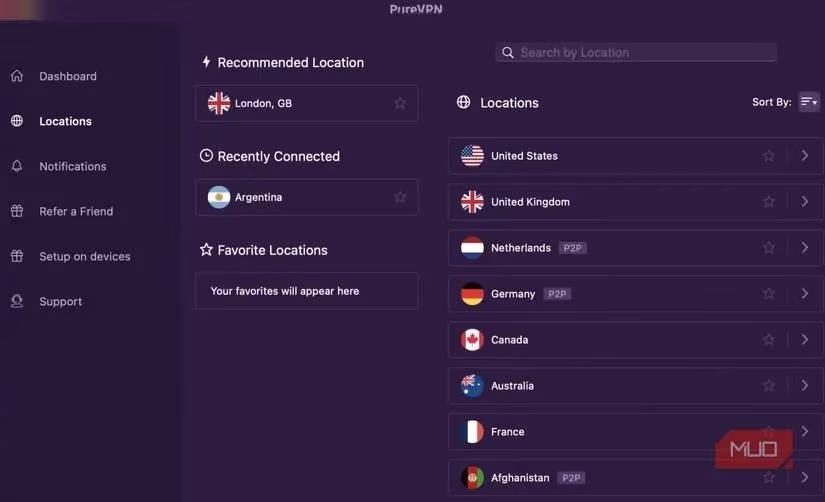
As users, we navigate the VPN marketplace believing in a vibrant ecosystem of independent contenders, each vying to offer the best protection. 😊 The reality, upon closer inspection, is one of significant consolidation under a few large corporate umbrellas. This revelation can feel like a breach of trust in itself.
Consider the following table of well-known providers and their corporate affiliations:
| VPN Provider | Parent Company / Major Shareholder |
|---|---|
| ExpressVPN | Kape Technologies (formerly Crossrider) |
| CyberGhost | Kape Technologies |
| Private Internet Access (PIA) | Kape Technologies |
| NordVPN | Tesonet (various allegations of shared infrastructure with other services) |
| Surfshark | Merged with NordVPN under Nord Security |
Discovering that three distinct, popular brands are owned by the same entity—Kape Technologies—can be jarring. It transforms a landscape of apparent choice into a selection from a handful of corporate strategies. The benefits of such consolidation are clear: financial stability, vast server networks, and shared technological development. However, the risks are palpable:
-
Homogenization of Policies: A move towards uniform privacy policies and data-handling practices across brands.
-
Prioritization of Market Control: The primary driver may shift from user-centric innovation to market dominance and shareholder value.
-
Single Point of Scrutiny: A privacy scandal or security failure at the parent level could implicate all its subsidiary services.
Rebuilding Trust in a Transparent Future
So, where does this leave the privacy-seeking individual in 2026? Cynicism is not the answer, but informed, vigilant trust is the new requirement. The path forward for both users and the industry must be paved with radical transparency and verifiable action.
For a VPN provider to earn trust today, it must move beyond vague promises. The new gold standard includes:
-
Alignment of Policy and Expectation: A no-logs policy must be written in clear, unambiguous language that matches what a typical user understands it to mean. Jargon and loopholes must be eliminated.
-
Regular Independent Audits: Claims must be validated not by marketing copy, but by rigorous, public audits from respected third-party firms. A one-time audit is a start; continuous, periodic audits are the standard.
-
Embracing Open-Source Principles: There is a growing and compelling argument for open-source VPN software. When code is transparent and can be examined by the global security community, it builds a foundational layer of trust that proprietary software struggles to match.
-
Jurisdictional Clarity: Operating under the legal framework of a privacy-respecting country (like Panama, the British Virgin Islands, or Switzerland) is a significant factor, as it reduces the risk of mandatory data retention laws.
This evolving landscape is why providers like Mullvad VPN have garnered intense respect from the privacy community. With its radical transparency, open-source clients, acceptance of anonymous cash payments, and a publicly verifiable no-logs infrastructure, it represents a philosophy where privacy is engineered into the service, not just marketed on top of it.
Conclusion: Beyond the One-Click Illusion
The journey through the VPN landscape in 2026 is a sobering one. It teaches that a VPN is not a magical, one-click privacy talisman. It is a tool—a potentially powerful one—but its efficacy is entirely dependent on the integrity and transparency of the hands that built it. The scandals of the past have not destroyed the value of VPNs; they have instead forged a more discerning user and, hopefully, a more accountable industry.
The quest for digital privacy is perpetual. It requires us to look past the shiny interface and the bold claims, to question corporate structures, to demand proof, and to understand that true security is a layered endeavor. In this light, choosing a VPN becomes less about finding an impenetrable fortress and more about selecting a trustworthy guide for your journey through the watched wilderness of the modern internet. The veil, it turns out, must be woven with threads of transparency, audited integrity, and aligned purpose, lest it become merely another filter through which we are seen.
This perspective is supported by reporting from The Verge - Gaming, whose industry analysis helps contextualize how “no-logs” VPN promises can clash with real-world incentives like corporate consolidation and data retention practices. Read alongside the concerns raised in this blog, their coverage underscores a practical takeaway: a VPN shifts trust rather than eliminating it, making audits, transparent ownership, and clearly defined metadata policies essential parts of any privacy-minded setup.
