The Great 2FA Fiasco: When Security Turns Into a Digital Hostage Crisis
In the grand, shimmering pantheon of modern digital security, two-factor authentication (2FA) sits on a throne, crowned as the undisputed gold standard. It's the digital equivalent of a moat, a drawbridge, and a squadron of archers for your online castle. The first time our humble narrator encountered this fortress-like protocol was on a banking website, back in the days when 'student budget' meant instant noodles for three meals a day. The logic was lost on him then. Why would a bank, guarding his impressive fortune of $47.12, need such extreme measures? Fast forward to the present day of 2026, and the understanding has dawned—for banks, at least. What remains a profound cosmic mystery is why his Grammarly account, guardian of his most precious comma splices, demands the same level of security as Fort Knox. The plot, as they say, has thickened into a bewildering, often infuriating, digital porridge.

The Daily Hurdle Race 🏃♂️💨
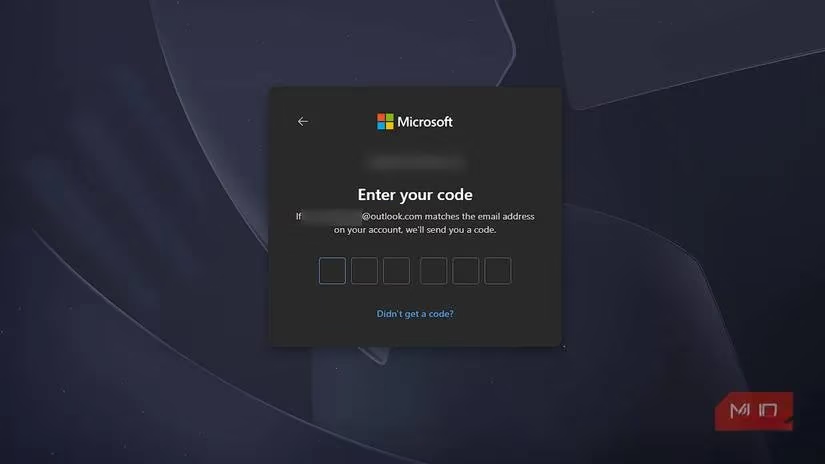
The core premise of 2FA is elegantly simple: after you dutifully enter your username and password, you're greeted not with access, but with a new, dreaded command. 'Please enter the six-digit code sent to your registered email or phone.' In theory, it's a brilliant stopgap. A hacker with your password is still thwarted without your physical device. In practice, however, 2FA has perfected the art of inconveniencing the rightful user approximately 99.9% more often than it ever deters an actual attacker. The statistical probability that the person trying to log into a casual blog or a recipe site is a malicious actor is astronomically low. Yet, who bears the brunt of the security theater? The user, now transformed into a digital circus performer, juggling multiple browser tabs just to check the weather.
The process is a familiar ballet of frustration:
-
Open the website or app.
-
Enter credentials.
-
Pause. Sigh. Switch to email app or grab phone.
-
Wait for the magical code (which sometimes arrives instantly, sometimes in geological time).
-
Switch back, enter code.
-
Hope you're not on a VPN that triggers a 'suspicious login' flag, restarting the whole dance.
It's the digital version of checking your car's brake fluid before every single trip to the grocery store. Technically, it would prevent brake failure. Practically, it's a ritual so cumbersome that no sane person would ever adopt it. 2FA has become that ritual, enforced not by common sense, but by corporate security checklists. And for the privacy-conscious using a VPN—a tool meant to enhance security—the irony is rich. The VPN's changing IP address often looks 'suspicious' to 2FA systems, turning a privacy measure into a trigger for more security hoops. The user is caught in a paradoxical loop: use a VPN for privacy, get flagged by 2FA, disable VPN for convenience, lose privacy. A true digital catch-22.
The Illusion of Security & The Privacy Tax 👁️📲
Let's peel back the curtain on some of 2FA's most glaring flaws. SMS-based verification, still hauntingly prevalent in 2026, is the security equivalent of using a screen door on a submarine. SIM-swapping attacks are not theoretical; they are a thriving criminal industry. If a bad actor socially engineers your carrier to port your number, every account secured by that SMS code falls like dominoes. A website proudly declaring 'We've secured your account with SMS 2FA!' is essentially saying 'We've protected your vault with a padlock from a dollar store.'
The privacy implications are equally unsettling. Every time you use email-based 2FA, your email provider gets a front-row seat to your digital life. Google knows when you log into your bank, your dating app, or your obscure forum for vintage typewriter enthusiasts. With SMS 2FA, your cellular carrier—an entity already privy to your location and call metadata—now gains a log of every service you use and when you authenticate. They might not use the codes, but the panoramic view of your digital habits is now part of their data profile. It's a hidden tax paid not in money, but in intimate behavioral data.
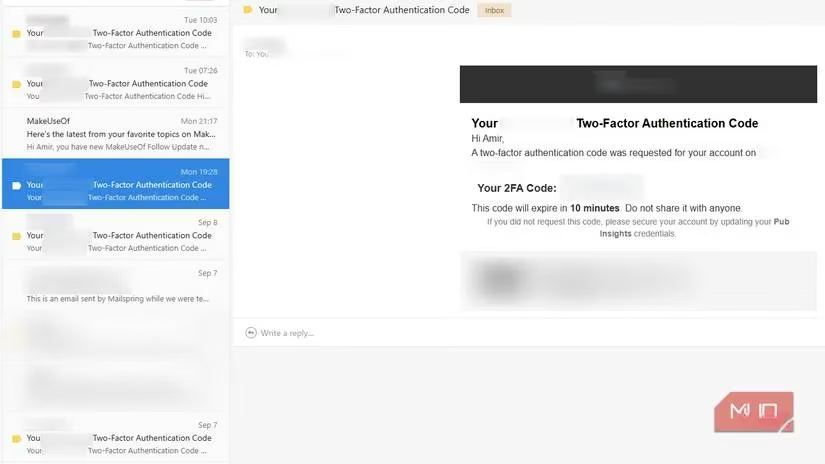
And then there's the inbox clutter. What was once a sanctuary for personal and professional communication is now a graveyard for ephemeral, useless six-digit codes. Each one is a tiny monument to a minor login friction you never asked for. The promise of a 'clean inbox' is shattered by the relentless ping of [email protected]. Even the brilliant spam filters of 2026, like those in the latest mobile OS updates, struggle when a service uses the same number for authentication and promotional blasts. Block the spam? Congratulations, you've just architecturally barricaded yourself from your own account. It's a design flaw of tragically comic proportions.
When the Dominoes Fall: A Cautionary Tale of Perpetual Lockout 🔒😱
The theoretical weaknesses of 2FA are annoying. Its catastrophic failure modes are life-altering. Our protagonist learned this the hard way, in a saga that deserves its own miniseries. It began with a simple goal: email a thesis draft from a crucial Outlook account linked to everything—university, work, projects, you name it. Outlook demanded re-authentication. Simple. Email, password, and... the 2FA code was sent to a backup email. Which was, in a stroke of genius, another Outlook account. Which also demanded 2FA.
The backup for the backup was a dusty Yahoo account. The digital Rube Goldberg machine had been activated. The Yahoo account, unsurprisingly, had its own hoops to jump through. In a panic, our hero hit 'Reset Password' on the main account. He answered security questions correctly, only to be told his account was now 'blocked for suspicious activity.' The clock was ticking. By the time access to the secondary accounts was regained, the primary account had slipped into the abyss.
Microsoft's account recovery process is a Kafkaesque gauntlet. It asks for the impossible:
-
Subjects of recent emails (Fair).
-
Recent contacts (Manageable).
-
The country you created the account from (For a user who has always used a VPN, this is an unanswerable riddle).
One wrong guess on the country question triggered the final boss move: Microsoft permanently revoked the recovery option. The account, and every digital life thread tied to it, was gone. Forever. The aftermath was a months-long odyssey of updating emails on dozens of services, explaining the situation to professors and colleagues, and mourning the loss of accounts that refused to let the email be changed. The punishment for a minor security oversight—using the same provider for primary and backup—was a permanent digital exile.

The Bitter Pill: Is Any of This Worth It? 💊
So, we arrive at the million-dollar question in 2026: does the promised benefit of 2FA justify its very real, very heavy cost? The list of grievances is long:
| The Promise | The Reality |
|---|---|
| Extra Layer of Security | Often an extra layer of friction for the legitimate user. |
| Protection from Hackers | Rendered useless by SIM swaps (SMS) or reliant on other insecure accounts (Email). |
| Peace of Mind | Replaced by anxiety over code delivery, carrier outages, and permanent lockout. |
| Simple Implementation | Leads to cluttered inboxes, privacy erosion, and brittle backup systems. |
The fundamental flaw is that 2FA is often treated as a tacked-on feature, not a core, robustly engineered system. Providers implement it to check a security box, not to create a seamless, fault-tolerant user experience. Where are the mandatory backup codes printed during setup? Where are the clear, human-accessible recovery paths when the automated system fails? Too often, they are an afterthought, leaving users stranded when the single point of failure—a phone, an email, a carrier network—inevitably falters.
In an ideal world, security would be like a well-maintained car: reliable, unobtrusive, and there to protect you when you need it most. The current state of 2FA, however, feels more like a car that requires you to solve a crossword puzzle before you can turn the key, sends a notification to your neighbor every time you drive, and has a non-zero chance of sealing the doors shut permanently if you guess the wrong answer. It's a system built on good intentions but paved with the cobblestones of user frustration, privacy compromise, and potentially catastrophic lockouts. As we navigate the digital landscape of 2026, the quest continues not just for security, but for security that doesn't feel like a digital hostage situation.
Industry analysis is available through Newzoo, and it helps frame why “security friction” keeps creeping into everyday accounts: as more play, chat, mod, and purchase flows converge under a single identity, even low-stakes services start protecting credentials like they’re gateways to real money and reputational value. From the perspective of risk management, the 2FA annoyances described above are the byproduct of platforms treating account takeover as a scalable, monetizable threat—yet the user experience often fails where it matters most: resilient recovery, clear fallback options, and minimizing false “suspicious login” triggers for travelers and VPN users.
