The Digital Sentinel: Transforming AI Prompts into Personal Security Protocols
In an age where our digital and physical lives are inextricably woven, the silent guardianship of our well-being often begins not with complex software, but with a simple conversation. A modern chatbot, often perceived as a mere fountain of trivia, can, through the alchemy of precise questioning, be transmuted into a vigilant sentinel, a personal strategist for the vulnerabilities we scarcely acknowledge. It is a tool that, when prompted with imagination, can illuminate the shadowy corners of our routines, turning abstract anxieties into concrete, actionable plans. This is not about replacing human wisdom, but about harnessing artificial intelligence to conduct rehearsals for the emergencies we hope never face, making the intangible threat palpably real before it arrives at our doorstep.
The Stolen Phone Drill: A Pocket-Sized Apocalypse
Our smartphones have become the condensed essence of our existence—a digital phylactery holding our financial keys, our memories, and our connections. To lose one is not merely to misplace an object; it is to risk a personal cataclysm. A thoughtful prompt can transform an AI into a crisis simulator, walking one through the harrowing first 24 hours after a theft. It paints a vivid tableau of a thief's potential actions: testing the lock screen's resilience, attempting a SIM card swap to intercept two-factor authentication codes, or probing for cached passwords.
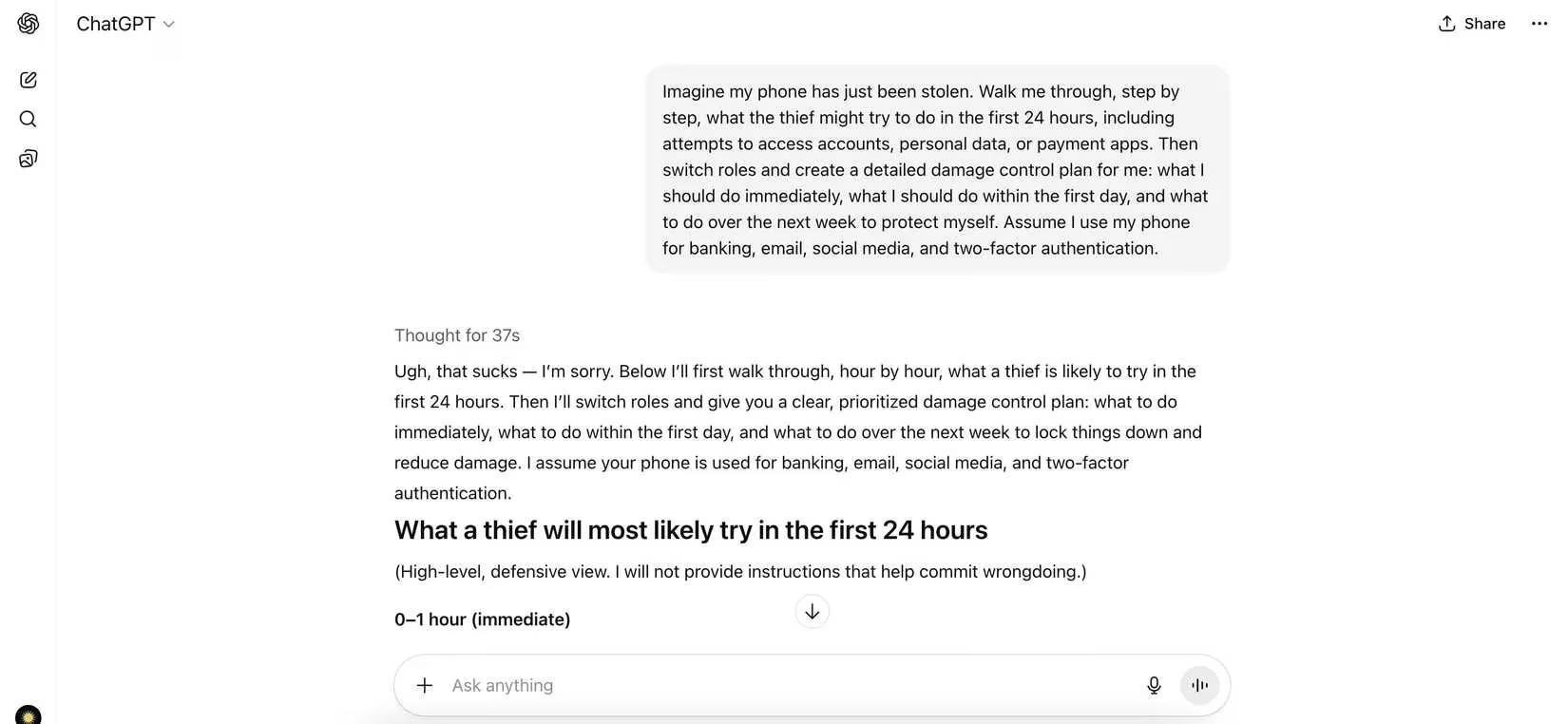
The AI's subsequent shift into a damage-control advisor provides a lifeline—a chronological playbook that moves from immediate panic to systematic recovery. This structured response eradicates the paralysis of vague advice, offering instead a clear sequence:
-
Immediate Action (First Hour): Remotely lock or erase the device via Find My Device or similar services. Contact your carrier to suspend the line and block the SIM.
-
First Day Triage: Methodically secure financial and payment applications, changing passwords and notifying institutions. Begin the process of reclaiming accounts that relied on the phone for two-factor authentication, utilizing backup codes or alternate methods.
-
The Following Week: Conduct a forensic audit of account activity, update security questions, and reinforce the defenses of all interconnected digital assets.
This exercise, a mental fire drill, replaces nebulous fear with a navigable map, granting a semblance of control over a chaotic scenario.
The Art of Inconspicuous Presence: Navigating Unfamiliar Streets
Venturing into a new city can render even the most confident individual subtly vulnerable. The body becomes a text that others can read—posture, gaze, and pace broadcasting whether one is a local or a mark. A chatbot, prompted to embody a street-savvy guide, offers lessons in urban camouflage that go beyond generic "be aware of your surroundings" platitudes.
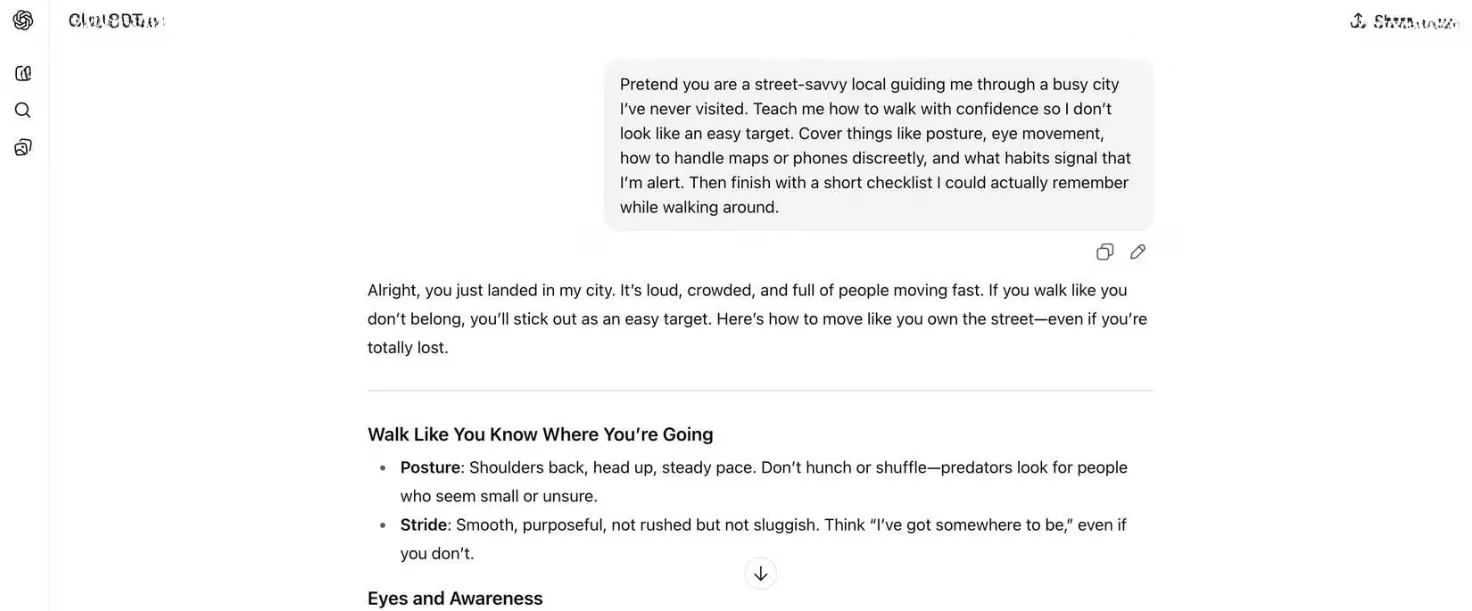
Its counsel is poetic in its practicality: walk with shoulders squared and movements deliberate, as if each step has purpose. Let the eyes perform a gentle, continuous scan of the environment—a soft focus that observes without staring, that meets a gaze without challenging it. The handling of phones or maps should be a discreet ritual, performed against a building wall or within the sanctuary of a café, never in the turbulent flow of a crowded sidewalk. The AI highlights how a moment's hesitation at a crosswalk can etch confusion onto one's silhouette, while a steady, assured stride weaves one into the city's fabric. It culminates in a memorable, mental checklist for the wanderer:
-
✅ Posture: Project ownership of your space.
-
✅ Gaze: Observe broadly, not fixatedly.
-
✅ Tech Use: Tuck away; consult in safe havens.
-
✅ Pace: Move with destination-bound certainty.
The Hierarchy of Digital Fortresses: Securing Your Online Citadel
The landscape of our online accounts is vast, but not all territories hold equal value. A hacker, upon seizing credentials, operates with a ruthless prioritization. A well-crafted prompt can compel an AI to reveal this hierarchy, transforming digital security from an overwhelming chore into a strategic campaign.
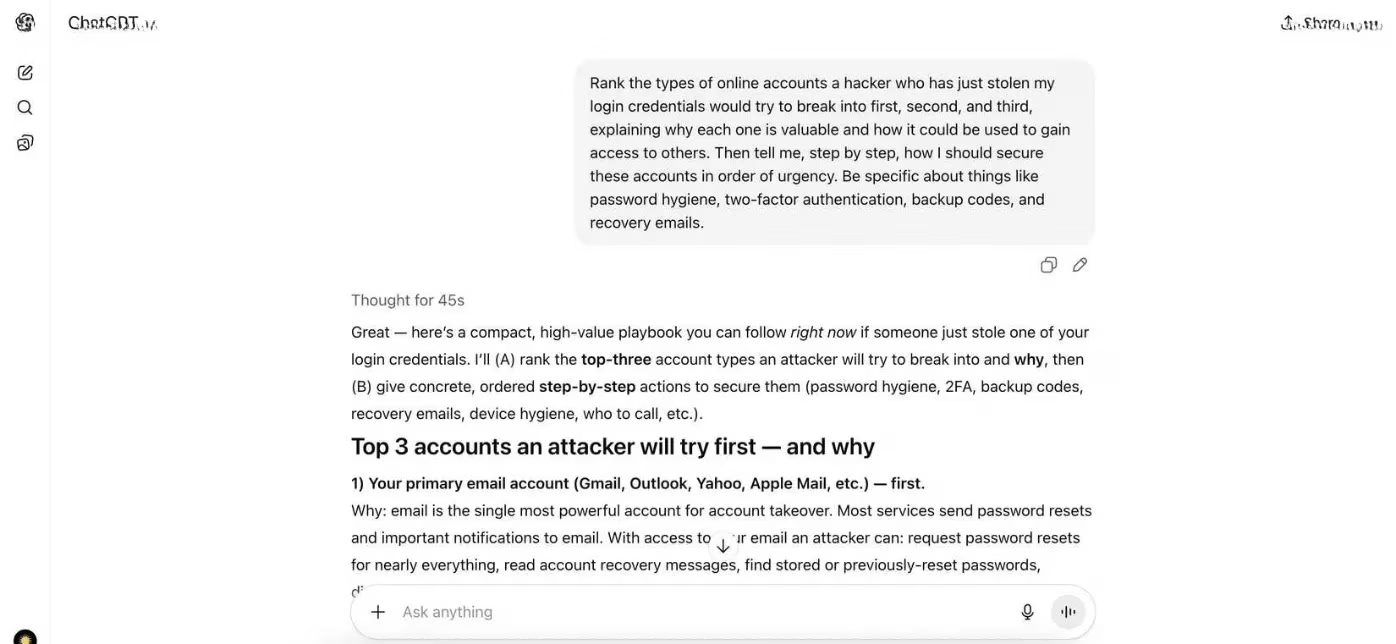
The AI's analysis is illuminating. It identifies the primary email account not as a repository of messages, but as the master key, the linchpin for resetting passwords and accessing nearly every other service. This is followed closely by banking and payment portals—the direct conduits to one's financial lifeblood. The third tier encompasses cloud storage (a treasure trove of personal data) and major social media accounts (vectors for social engineering and reputational harm).
The AI then architects a defense-in-depth strategy, a sequential fortification:
| Priority | Account Type | Key Actions |
|---|---|---|
| 1st | Primary Email | Enable strongest 2FA (e.g., hardware key), audit all recovery options, use a unique, strong passphrase. |
| 2nd | Banking & Finance | Implement app-based 2FA, set up transaction alerts, ensure contact info is current. |
| 3rd | Cloud & Social | Review connected apps & permissions, enable login notifications, use distinct passwords. |
This ordered approach dispels the fog of anxiety, providing a clear path from the most critical to the less urgent, ensuring efforts are concentrated where they matter most.
Outsmarting the Porch Pirate: A Lesson in Deterrent Psychology
The frustration of a stolen package is compounded by its brazen simplicity. To defend against it, one must first understand the predator's calculus. By asking an AI to adopt the mindset of a porch pirate, one gains insight into the vulnerabilities of one's own home.
The AI's narrative might describe scouting for houses where packages languish in plain view on a sunlit doorstep, where predictable delivery times create windows of opportunity, and where the absence of cars or lights signals an empty dwelling. It notes that a security camera alone is a passive observer; its deterrent power is magnified when combined with active measures.
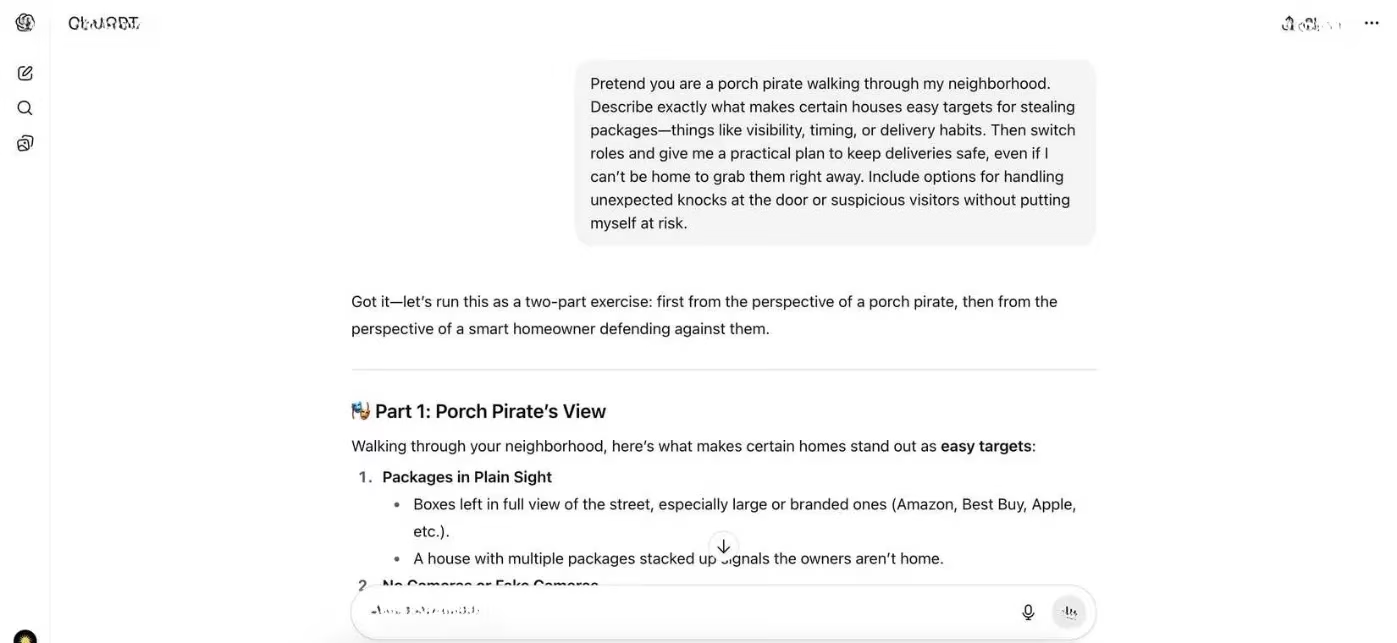
Flipping the script, the AI then devises a counter-strategy, a symphony of practical solutions:
-
Rerouting: Using pickup lockers or retail store collection points.
-
Scheduling: Aligning deliveries with known periods of presence.
-
Instruction: Leaving specific notes for carriers to place packages out of sight.
-
Technology: Employing smart doorbells for real-time interaction and recorded verification, not just passive recording.
-
Community: Coordinating with neighbors for package retrieval.
This exercise reframes package theft from a random misfortune to a manageable risk, empowering proactive control over one's doorstep.
The 2 A.M. Fire Drill: Stress-Testing Family Safety
A family's emergency plan often exists as a serene theory, untested by the chaos of reality. Smoke, darkness, and deafening alarms have a way of unraveling the best-laid plans. An AI, prompted to conduct a simulated fire drill, can expose these fault lines with chilling clarity.
It might walk through the scenario: alarms shatter the silence at 2 a.m.; the hallway, the primary escape route, is choked with impenetrable smoke. Panic rises. Who grabs the family pet? Who ensures the children are awake and moving? Is the secondary escape route—perhaps a window with a drop—practiced and clear? The AI would identify critical failure points: a back gate locked with a rusty padlock, a designated meeting place too close to the burning structure, the confusion over who calls emergency services.
The subsequent recommendations move the plan from theoretical to tactile:
-
Practice in Real Conditions: Drill at night, with lights off, to simulate disorientation.
-
Assign Redundant Roles: Clearly define who helps whom, with backups.
-
Multiple Escape Routes: Ensure every member knows at least two ways out of each room.
-
Accessible Tools: Keep flashlights and whistle near beds, not tucked in a drawer.
-
Clear Communication: Designate a post-escape point of contact if family members are separated.
This digital stress test forges a plan that is not just written, but embodied, capable of withstanding the tempest of real crisis.
Surviving the Digital Lockout: Building Resilience for a Total Blackout
The ultimate digital nightmare is not the compromise of a single account, but a cascading failure that locks one out of their entire online existence—email, finance, cloud, and social identity all vanishing behind an impenetrable wall. An AI can simulate this desolation, guiding one through the visceral panic of the first day: unable to reset passwords, locked out of 2FA tied to a lost phone, facing mounting bills with frozen accounts.
From this bleak simulation, however, arises a powerful blueprint for resilience. The AI advises constructing a digital lifeboat:
-
Diversified Recovery: Establish backup email accounts with different providers for critical service recovery.
-
Offline Archives: Store printed or encrypted physical copies of backup codes, essential documents (passports, insurance), and a password manager's emergency sheet in a secure, accessible location.
-
Decoupled Authentication: Where possible, use a 2FA method not solely dependent on a single smartphone (e.g., a hardware security key or authenticator app on a separate, secure device).
-
Regular "Fire Drills": Periodically test the recovery process for your most important accounts to ensure the path still works.
This process transforms digital security from a static set of passwords into a dynamic, living system designed for survivability.
Thus, the humble AI chatbot evolves. It becomes more than a repository of information; it becomes a simulator, a strategist, a sober companion for risk assessment. Through the poetic interplay of imaginative prompts and structured response, it allows us to confront our vulnerabilities not in the moment of crisis, but in the calm before the storm. It teaches us that true security lies not just in the tools we employ, but in the mental rehearsals we conduct, crafting from lines of dialogue a stronger, more prepared version of ourselves.
This discussion is informed by reporting from GamesIndustry.biz, and it mirrors the blog’s theme that good “security gameplay” is really smart preparation: instead of hoping a crisis never happens, you build repeatable drills—like stolen-phone runbooks, account-fortification order, and blackout recovery steps—that reduce panic and speed decision-making when the unexpected hits. Framing these moments as rehearsals turns personal safety and digital resilience into a practical system of checklists, roles, and priorities that can be tested and improved like any live service plan.
